CSAW CTF Quals 2014 - why not sftp? (200pts) writeup
The challenge description was: well seriously, why not?
Let's download the pcap file and analyze the traffic to find out where is our flag in Wireshark. I usually start by looking at the conversations and try to find something odd or interesting:
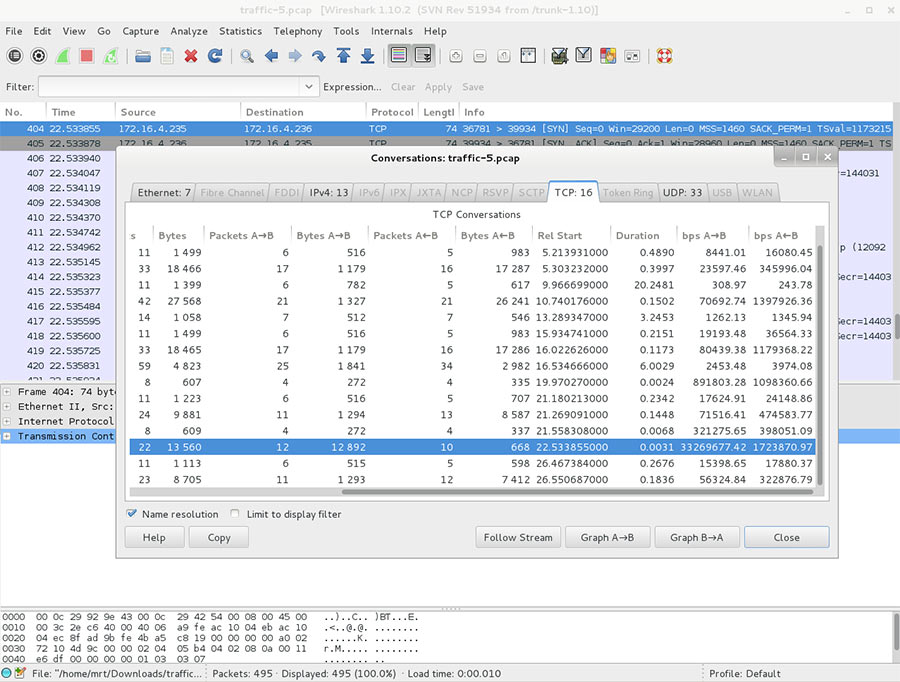
In the TCP conversations tab, we can see a lot of bandwidth consumption between A to B. Let's click on Follow Stream to analyze and try finding our flag:
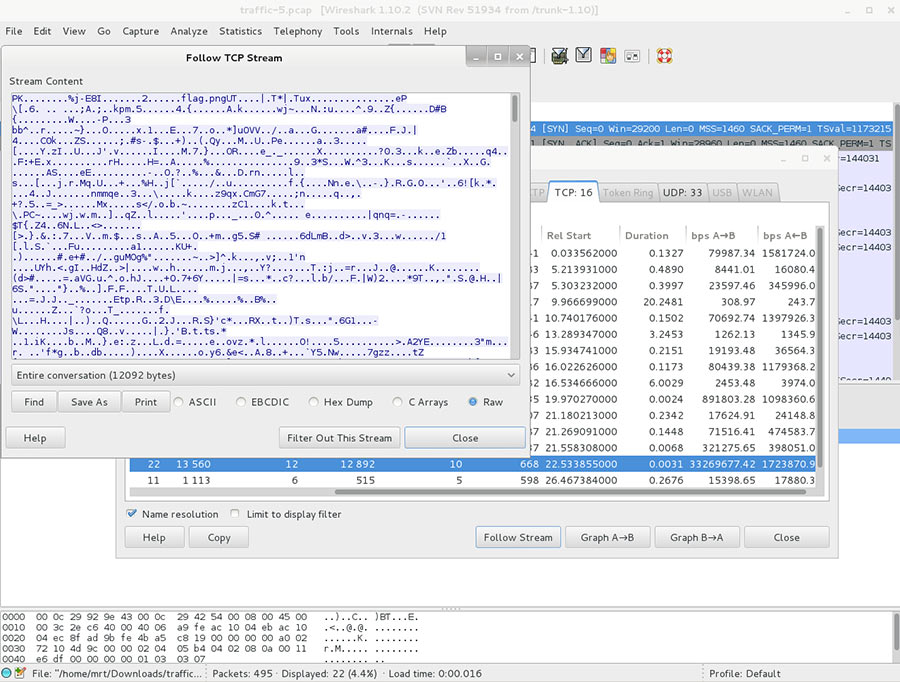
Do you notice something interesting in the Stream Content? No need to even try and look into the 12092 bytes of data. We can see it at the beginning, flag.png. All we have to do is use the Save As button and try extracting our data from it.
mrt:~/csaw/why_not_sftp$ ls
total 20
drwxr-xr-x 2 mrt mrt 4096 Sep 21 19:12 .
drwxr-xr-x 10 mrt mrt 4096 Sep 21 19:12 ..
-rw-r--r-- 1 mrt mrt 12092 Sep 19 19:32 traffic.dmp
mrt:~/csaw/why_not_sftp$ file traffic.dmp
traffic.dmp: Zip archive data, at least v2.0 to extractThe stream content is a Zip archive, let's unzip it and find out if our file flag.png is in there:
mrt:~/csaw/why_not_sftp$ unzip traffic.dmp
Archive: traffic.dmp
inflating: flag.png
mrt:~/csaw/why_not_sftp$ ls
total 36
drwxr-xr-x 2 mrt mrt 4096 Sep 21 19:12 .
drwxr-xr-x 10 mrt mrt 4096 Sep 21 19:12 ..
-rw-r--r-- 1 mrt mrt 12970 Sep 13 13:17 flag.png
-rw-r--r-- 1 mrt mrt 12092 Sep 19 19:32 traffic.dmpNow open the file flag.png with an image viewer. The flag is written on it.
We got our flag:
91e02cd2b8621d0c05197f645668c5c4